Transparent Data Encryption (TDE) is another new feature in SQL Server 2008. It performs real-time I/O encryption and decryption of the data and log files, that is the entire database. For achieving that, it uses a database encryption key stored in the database boot record.
A derived benefit of TDE is that whenever a database using TDE is backed up, the backup set is also encrypted.
All of the above provide significant data security in SQL Server 2008.
The Procedure to Encrypt (TDE) a Database in SQL Server
The procedure for encrypting a database is provided below by T-SQL Code example:
USE master GO --Step 1: Create a Master Key CREATE MASTER KEY ENCRYPTION BY PASSWORD = 'password_goes_here'; GO --Step 2: Create or obtain a certificate protected by the master key CREATE CERTIFICATE MyServerCert WITH SUBJECT = 'MyCertificate' GO --Step 3: Create a database encryption key and protect it by the certificate USE [DATABASE_NAME] GO CREATE DATABASE ENCRYPTION KEY WITH ALGORITHM = AES_128 ENCRYPTION BY SERVER CERTIFICATE MyServerCert GO --Step 4: Set the database to use encryption ALTER DATABASE [DATABASE_NAME] SET ENCRYPTION ON GO
After the above are performed, the database will enter the “Encrypted” state.
Remarks and Considerations
1. Important note regarding TDE: When enabling TDE, you should immediately back up the certificate and the private key associated with the certificate . This is absolutely necessary when trying to restore or attach the encrypted database on another server because you will need to use these keys and certificates. In the opposite case the database will not be accessible. Additionally the encrypting certificate should be retained even if TDE is no longer enabled on the database as it may need to be accessed for some operations.
2. Steps 3 and 4 can be performed from within SQL Server 2008 Management Studio by right-clicking on the database and selecting Tasks –> Manage Database Encryption.
3. Note that four encryption are currently provided:
AES_128
AES_192
AES_256
Triple_DES
4. The entire TDE on a database is completely transparent to the user as it is performed in the background and on the fly.
More information regarding Transparent Data Encryption in SQL Server 2008 can be found in the following link.
Also, if we wish to check out a list we prepared with the “10 Facts About SQL Server Transparent Data Encryption“, feel free to check out the relevant article.
Strengthen your SQL Server Administration Skills – Enroll to our Online Course!
Check our online course on Udemy titled “Essential SQL Server Administration Tips” (special limited-time discount included in link).
Via the course, you will learn essential hands-on SQL Server Administration tips on SQL Server maintenance, security, performance, integration, error handling and more. Many live demonstrations and downloadable resources included!
Learn essential SQL Server development tips! Enroll to our Online Course!
Check our online course titled “Essential SQL Server Development Tips for SQL Developers” (special limited-time discount included in link).
Sharpen your SQL Server database programming skills via a large set of tips on T-SQL and database development techniques. The course, among other, features over than 30 live demonstrations!

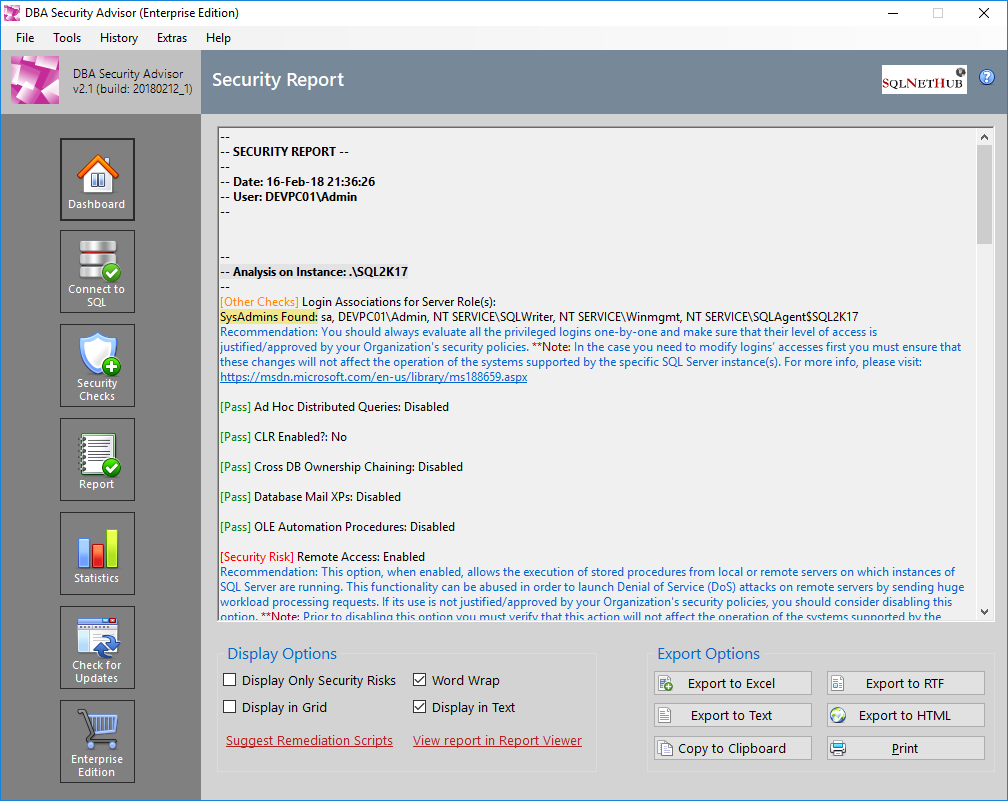
Secure your SQL Server Instances with DBA Security Advisor
DBA Security Advisor, is our SQL Server security tool, which can help you assess your SQL Server instances against a rich set of security checks. The assessment report, includes recommendations and remediation scripts that can help you better secure your SQL Server instances and databases (learn more…).
Try DBA Security Advisor free for 7 days!
Featured Online Courses:
- SQL Server 2022: What’s New – New and Enhanced Features
- Working with Python on Windows and SQL Server Databases
- Introduction to Azure Database for MySQL
- Boost SQL Server Database Performance with In-Memory OLTP
- Introduction to Azure SQL Database for Beginners
- Essential SQL Server Administration Tips
- SQL Server Fundamentals – SQL Database for Beginners
- Essential SQL Server Development Tips for SQL Developers
- Introduction to Computer Programming for Beginners
- .NET Programming for Beginners – Windows Forms with C#
- SQL Server 2019: What’s New – New and Enhanced Features
- Entity Framework: Getting Started – Complete Beginners Guide
- Data Management for Beginners – Main Principles
- A Guide on How to Start and Monetize a Successful Blog
Other SQL Server Security-Related Articles
- DBA Security Advisor v2.3 is Now Out!
- Frequently Asked Questions about SQL Server TDE
- How to Enable SSL Certificate-Based Encryption on a SQL Server Failover Cluster
- Why You Need to Secure Your SQL Server Instances
- Policy-Based Management in SQL Server
- Should Windows “Built-In\Administrators” Group be SQL Server SysAdmins?
- Frequent Password Expiration: Time to Revise it?
- The “Public” Database Role in SQL Server
- Encrypting SQL Server Databases
- 10 Facts About SQL Server Transparent Data Encryption
- Encrypting a SQL Server Database Backup
- …check all
Subscribe to our newsletter and stay up to date!
Subscribe to our YouTube channel (SQLNetHub TV)
Check out our latest software releases!
Check out our eBooks!
Rate this article:
Reference: SQLNetHub.com (https://www.sqlnethub.com)
© SQLNetHub
Artemakis Artemiou, a distinguished Senior Database and Software Architect, brings over 20 years of expertise to the IT industry. A Certified Database, Cloud, and AI professional, he earned the Microsoft Data Platform MVP title for nine consecutive years (2009-2018). As the founder of SQLNetHub and GnoelixiAI Hub, Artemakis is dedicated to sharing his knowledge and democratizing education on various fields such as: Databases, Cloud, AI, and Software Development. His commitment to simplicity and knowledge sharing defines his impactful presence in the tech community.