Transparent Data Encryption known also known as TDE (learn more), encrypts SQL Server, Azure SQL Database and Azure SQL Data Warehouse data and log files on the OS-level. Moreover, a derived benefit is that also SQL Server-based backups of encrypted databases are also encrypted. This type of encryption can be characterized as encrypting data at rest. In other words, it encrypts stored data (storage can be persistent storage like a disk drive or tape).
In this article, I’m providing a list with 10 facts that you should definitely know about Transparent Data Encryption in SQL Server.
10 Facts about SQL Server Transparent Data Encryption (TDE):
- TDE is supported in SQL Server 2008 (Enterprise Edition only) or later, Azure SQL Database and Azure SQL Data Warehouse,
- When enabling TDE, you should immediately back up the certificate and the private key associated with the certificate to a safe location,
- Backup files of databases that have TDE enabled are also automatically encrypted by using the database encryption key,
- In SQL Server 2016 or later, backup compression for TDE-enabled databases is fully supported (learn more here),
- If even a single database on a SQL Server instance is encrypted using TDE, then the “tempdb” system database will be automatically encrypted too,
- By the time a single database is encrypted using TDE, and thus tempdb is automatically encrypted, this will have a performance effect for unencrypted databases too on the same SQL Server instance.
- FILESTREAM data is not encrypted even when TDE is enabled,
- Files related to buffer pool extension (BPE) are not encrypted when a database is encrypted using TDE,
- In SQL Server 2016 and later, as well as in Azure SQL Database In-Memory OLTP, log records and data are encrypted if TDE is enabled. However, in SQL Server 2014 In-Memory OLTP, only log records are encrypted if TDE is enabled since files in the MEMORY_OPTIMIZED_DATA filegroup are not encrypted,
- When you encrypt a database in SQL Server, Azure SQL Database or Azure SQL Data Warehouse, you do not need to do anything on the application-level because as the name of TDE implies, it is totally transparent and does not require any changes on the application.
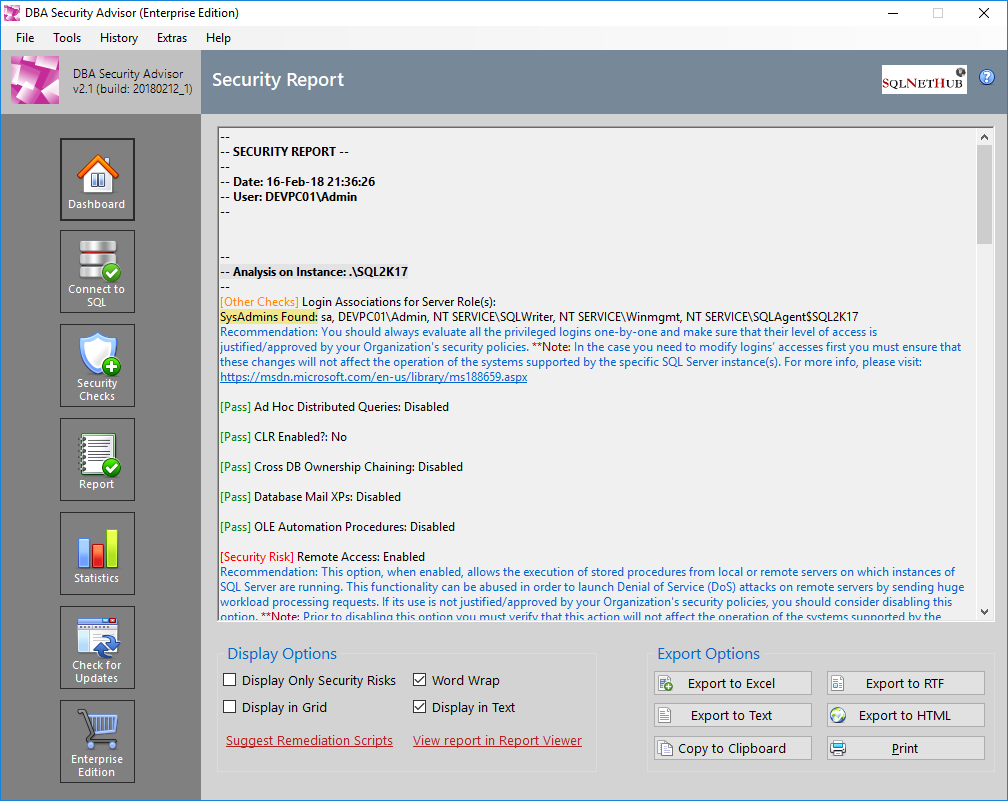
Secure your SQL Server Instances with DBA Security Advisor
DBA Security Advisor, is our SQL Server security tool, which can help you assess your SQL Server instances against a rich set of security checks. The assessment report, includes recommendations and remediation scripts that can help you better secure your SQL Server instances and databases (learn more…).
Try DBA Security Advisor free for 7 days
Strengthen your SQL Server Administration Skills – Enroll to our Online Course!
Check our online course on Udemy titled “Essential SQL Server Administration Tips” (special limited-time discount included in link).
Via the course, you will learn essential hands-on SQL Server Administration tips on SQL Server maintenance, security, performance, integration, error handling and more. Many live demonstrations and downloadable resources included!
Featured Online Courses:
- AI Essentials: A Beginner’s Guide to Artificial Intelligence
- SQL Server 2022: What’s New – New and Enhanced Features
- Working with Python on Windows and SQL Server Databases
- Introduction to Azure Database for MySQL
- Boost SQL Server Database Performance with In-Memory OLTP
- Introduction to Azure SQL Database for Beginners
- Essential SQL Server Administration Tips
- SQL Server Fundamentals – SQL Database for Beginners
- Essential SQL Server Development Tips for SQL Developers
- Introduction to Computer Programming for Beginners
- .NET Programming for Beginners – Windows Forms with C#
- SQL Server 2019: What’s New – New and Enhanced Features
- Entity Framework: Getting Started – Complete Beginners Guide
- Data Management for Beginners – Main Principles
- A Guide on How to Start and Monetize a Successful Blog
Other SQL Server Security-Related Articles
- How to Enable SSL Certificate-Based Encryption on a SQL Server Failover Cluster
- Why You Need to Secure Your SQL Server Instances
- Frequently Asked Questions about SQL Server TDE
- [DBNETLIB] [ConnectionOpen (SECDoClientHandshake()).] SSL Security Error – How to Resolve
- Should Windows “Built-In\Administrators” Group be SQL Server SysAdmins?
- SQL Server Row Level Security by Example
- Frequent Password Expiration: Time to Revise it?
- Policy-Based Management in SQL Server
- The “Public” Database Role in SQL Server
- Encrypting SQL Server Databases
- Transparent Data Encryption (TDE) in SQL Server
- Encrypting a SQL Server Database Backup
- …check all
Check our latest software releases!
Easily generate snippets with Snippets Generator!
Secure your databases using DBA Security Advisor!
Convert static T-SQL to dynamic and vice versa with Dynamic SQL Generator.
Rate this article:
Reference: SQLNetHub.com (https://www.sqlnethub.com)
© SQLNetHub
Artemakis Artemiou is a seasoned Senior Database and AI/Automation Architect with over 20 years of expertise in the IT industry. As a Certified Database, Cloud, and AI professional, he has been recognized as a thought leader, earning the prestigious Microsoft Data Platform MVP title for nine consecutive years (2009-2018). Driven by a passion for simplifying complex topics, Artemakis shares his expertise through articles, online courses, and speaking engagements. He empowers professionals around the globe to excel in Databases, Cloud, AI, Automation, and Software Development. Committed to innovation and education, Artemakis strives to make technology accessible and impactful for everyone.